We are excited to announce the release of IP restrictions for Terraform resources, now generally available in HCP Terraform. With this release, HCP Terraform introduces a new capability to define an approved list of IP addresses for both organization and agent access.
»HCP Terraform resource access
Terraform supports multiple ways to access and manage infrastructure, including organization-level access through the web UI, APIs, VCS integrations and Terraform agents. Authentication is handled through user credentials or personal access tokens, which authorize requests to the platform.
Previously, Terraform lacked a centralized way to restrict access to organizational resources based on IP address. As a result, all access through Terraform web UI, APIs, VCS workflows, or Terraform agents was permitted from any location by default, as long as valid credentials or tokens were used. This inability to enforce network access controls introduced significant risk — particularly for enterprises operating in highly regulated industries. As these organizations adopt stricter security and compliance requirements, they need greater control over where authentication tokens can be used.
Without a way to restrict token usage to specific IP addresses, tokens could theoretically be used from any location until expiration, creating a gap between existing security policies and Terraform agent authentication. This prompted the need for a new way to ensure that agent tokens are accepted only when requests originate from trusted, predefined IP addresses.
»Introducing IP allow lists for Terraform
To address this challenge, we are introducing a new organization-level setting to configure lists of IP addresses defined as CIDR (classless inter-domain routing) ranges. These ranges typically correspond to known network egress points, such as NAT gateway IPs or trusted VPC egress, making it easier to align Terraform access with existing network architectures:
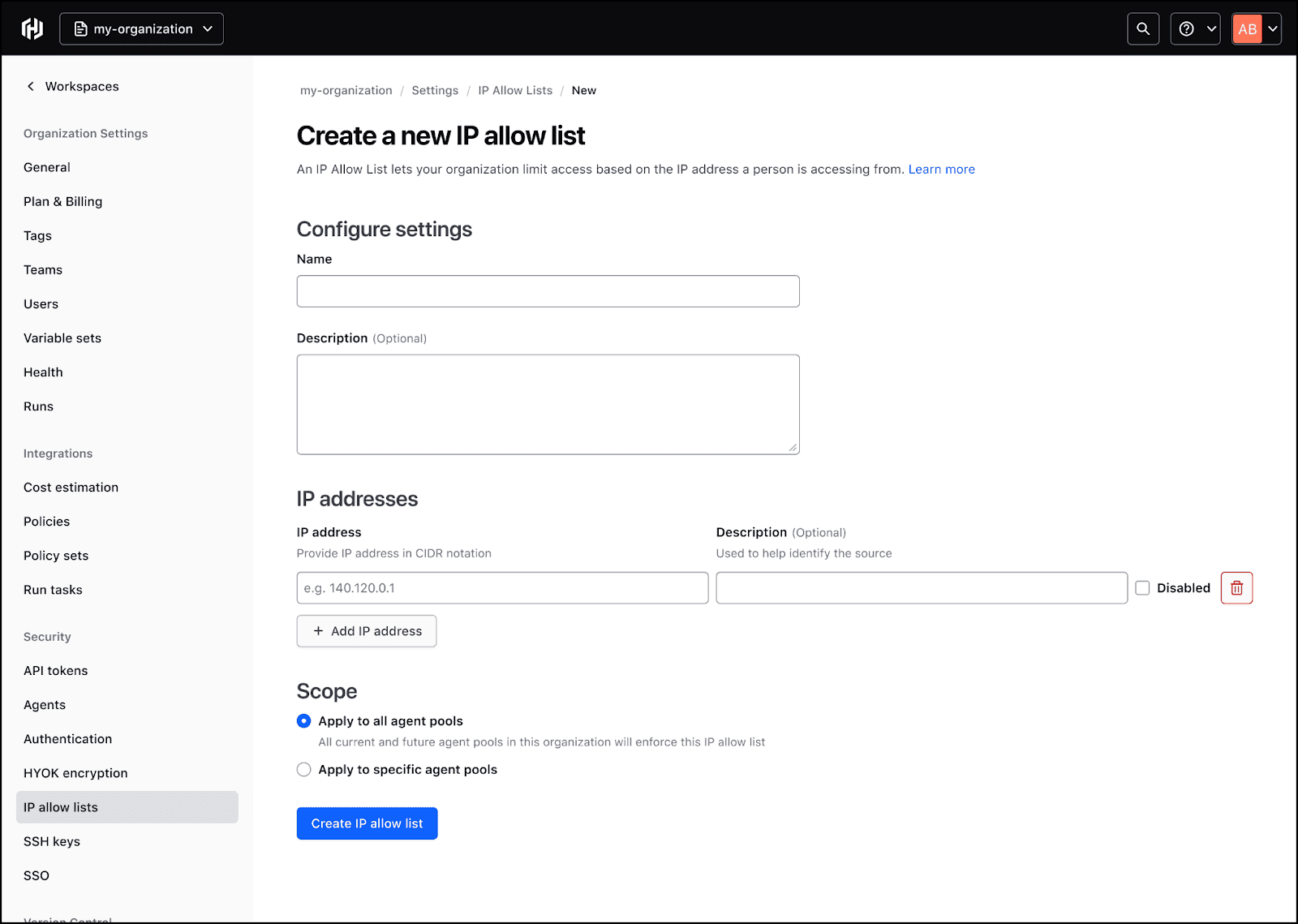
Create new IP allow lists and specify agent pools to apply to.
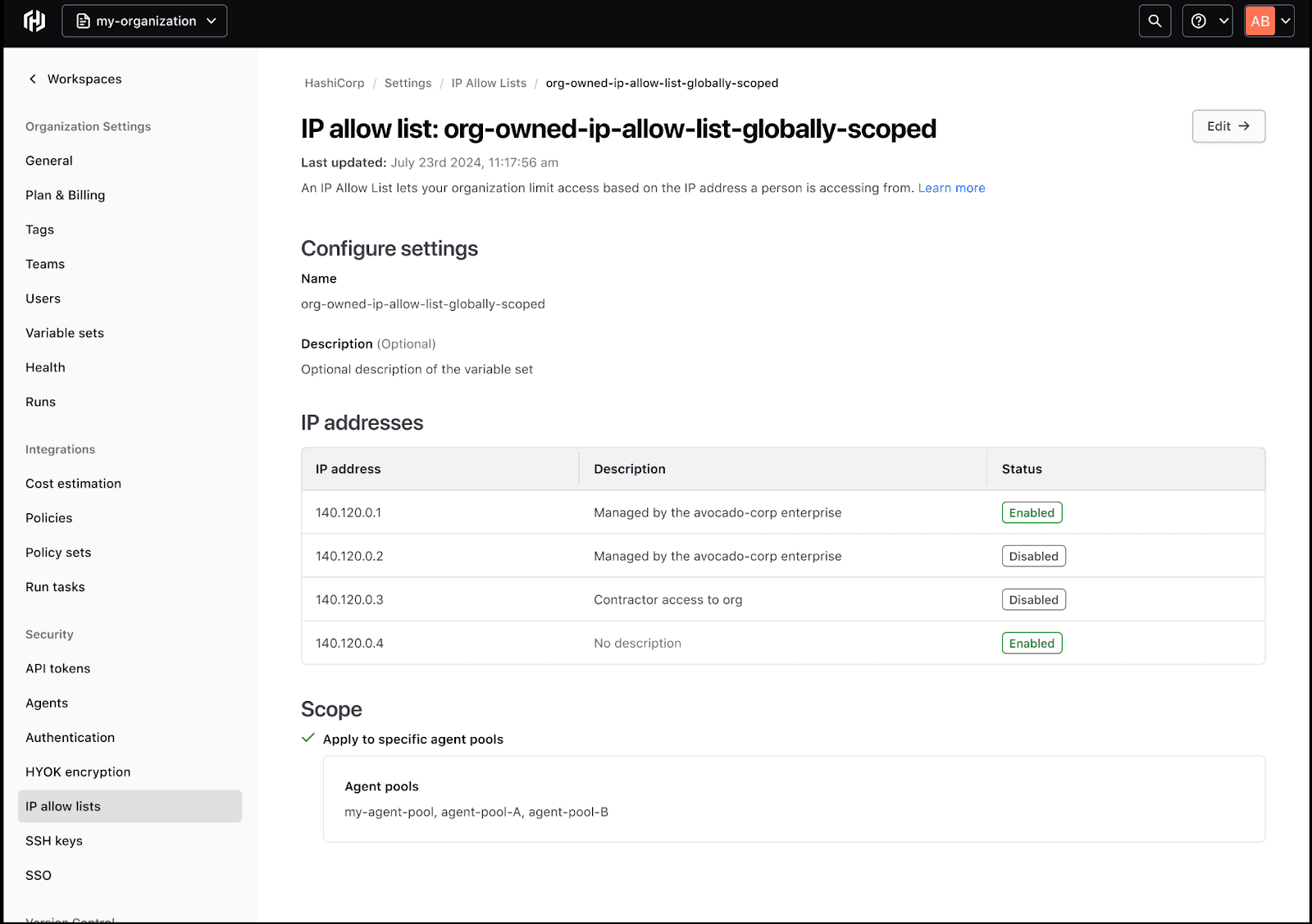
View a list of allowed IP addresses, who manages them, and status.
IP allow lists can be assigned to individual agent pools or all agent pools, giving admins flexibility in how they enforce network restrictions. Once configured, the following enforcement rules apply:
-
Only agent pool scoped allowlists are enforced on agents. The organization-level list covers users accessing the site via the API or UI.
-
When ranges are defined and scoped to one or more agent pools, requests are restricted to both the organization-level ranges and ranges defined for the agent pools.
-
Requests from agent pools that do not have any ranges scoped to them will remain unrestricted. Requests from unauthorized IP addresses will receive a 404 Not Found response.
By enforcing IP-based restrictions, organizations can significantly reduce blast radius in the event of credential exposure. Even if an agent token is compromised, it is effectively unusable outside the defined network perimeter, ensuring access is limited to trusted environments.
»Next steps
This feature is now available in HCP Terraform and coming soon to Terraform Enterprise. Please refer to the Terraform IP allow list documentation for details on getting started.
If you are new to Terraform, you can get started with HashiCorp-managed HCP Terraform free to begin provisioning and managing your infrastructure in any environment. And don’t forget to link your HCP Terraform and HashiCorp Cloud Platform (HCP) accounts for a seamless sign-in experience.