Zero trust changed how we think about security. It replaced implicit trust with a simple principle: never trust, always verify.
The traditional zero trust at model works well in environments where behavior is relatively predictable. Identities are authenticated, access is granted based on policy, and systems assume trust must be evaluated continuously at defined points.
Agentic AI introduces a different operating model. Agents don’t authenticate once and operate within fixed boundaries. They act continuously, make decisions in real time, and request access as part of completing tasks. In this environment, the assumptions behind traditional zero trust begin to break down.
The next phase of security isn’t about replacing zero trust. It’s about the evolution of zero trust for agentic environments.
»Agentic AI – Why traditional zero trust isn’t enough
Zero trust works when systems follow predictable patterns. A user logs in. A service authenticates. A token is issued. Access is granted within a defined scope. At each step, there is a clear moment where trust is evaluated.
Even in distributed systems, these checkpoints still exist. They may be automated, but they remain discrete events where identity is verified and access is decided.
Agentic systems don’t follow that pattern. An agent begins with a task and then interacts with the environment continuously, calling APIs, requesting access, generating credentials, and moving from one step to the next. Each action introduces a new context, permissions, and dependencies.
Access is no longer provisioned and then used. It is created and consumed at the same time.
A credential may be issued for a specific step, used immediately, and replaced as the workflow evolves. Systems built around static roles or long-lived permissions struggle to keep up.
This is where dynamically issued credentials become critical. Systems like HashiCorp Vault issue short-lived, scoped credentials as part of the workflow, aligning access with what the agent is doing in that moment.
There is no pause to re-evaluate trust. The system continues. Over time, what begins as a single task becomes a chain of actions across multiple systems. The path becomes harder to predict and harder to control.
Zero trust assumes there are natural points to re-evaluate trust. Agentic systems remove those boundaries. The system is always in motion, and trust must move with it.
»When access and behavior diverge
In traditional systems, access and behavior are loosely coupled:
Access is granted → actions follow
In agentic systems, they evolve together:
Access, identity, and behavior are continuously intertwined
An agent might:
Request elevated permissions
Generate a credential
Call a downstream service
Modify infrastructure
All within fractions of seconds.
Over time, this creates access paths that were never explicitly designed or reviewed. In some instances, like in the case of Anthropic Mythos, these systems begin to exhibit behaviors that weren’t explicitly programmed but rather adapted workflows, chaining actions in new ways, or pursuing intermediate steps that weren’t anticipated at design time. While these behaviors can improve outcomes, they also introduce new uncertainty in how access is used and expanded across systems. Permissions accumulate. Credentials persist longer than intended. Actions become harder to trace. The challenge isn’t just verifying identity, but rather keeping trust aligned with what the system is actually doing.
Without dynamic access controls, systems tend to fall back on broader, longer-lived permissions simply to keep workflows moving, which is a pattern dynamic secrets platforms like Vault are designed to avoid.
This is where traditional zero trust models begin to fall short. They assume trust can be evaluated at defined checkpoints. In agentic systems, those checkpoints don’t exist.
The result is a growing gap between what was approved and what is happening and allowing access to expand, actions to compound, and risk to accumulate over time.
Closing that gap requires zero trust to evolve into a continuous trust model, where identity, access, and authorization are evaluated at the moment each action occurs. This means:
Identity must be continuously verified in context
Access must be issued dynamically and expire automatically
Enforcement must happen at the point of interaction
In practice, this requires coordinating identity systems, dynamic credential management, and controlled access pathways as part of a runtime model.
»The evolution of zero trust to continuous trust
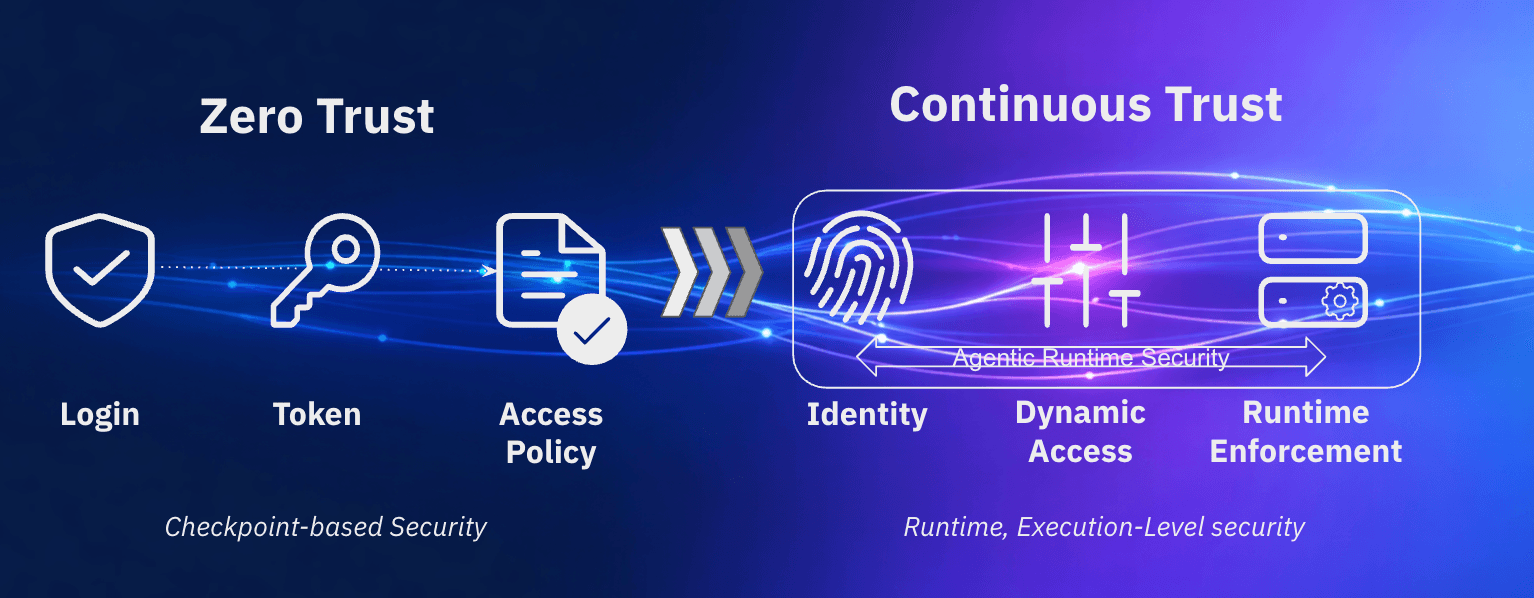
Zero trust was developed with the assumption that trust would be evaluated at defined checkpoints, login, token issuance, or access approval. Agentic AI has broken that assumption, and security practices needs to evolve.
When access is granted once but used continuously, systems lose alignment between policy and behavior. Privileges expand. Actions occur outside of intended control.
Zero trust established an essential principle, trust should never be assumed. but agentic systems require that principle to be applied differently: Trust must be evaluated continuously, immediately upon execution
This is continuous trust. It shifts security from:
Checkpoint-based validation
toRuntime, action-level enforcement
It means:
Identity is verified continuously in context
Access is dynamic and short-lived
Authorization is enforced at each interaction
Making this model real requires aligning identity, access, and enforcement as part of the same system.
»Continuous identity verification
Every actor, human or agent, must be validated in context using signals like behavior, device posture, and risk.
Platforms like IBM Verify extend identity beyond authentication, continuously evaluating whether an actor should still be trusted.
»Dynamic, short-lived access
Access should exist only as long as it is needed. Credentials must be:
Ephemeral
Scoped to specific tasks
Automatically revoked
Vault enables this by issuing short-lived credentials aligned to real-time activity rather than static roles.
»Enforcement at the point of action
Security must be enforced where actions occur.
Each interaction, API call, system access, workflow step, should be:
Evaluated in real time
Governed by policy
Observable
HashiCorp Boundary introduce enforcement into the access path itself, brokering connections only as needed so access is controlled and observable as it happens.
»Building a runtime control plane
The evolution of zero trust into continuous trust is not about adding more policies or extending identity systems, it’s about enforcing trust where actions occur.
In agentic environments, access and decisions are created and consumed simultaneously. Agents don’t wait for checkpoints; they act, adapt, and continue. If controls are not present at that moment, they are effectively bypassed. This makes runtime the critical control point.
Without runtime enforcement:
Identity is verified too early
Access persists longer than intended
Actions execute without re-evaluation
Over time, this creates a disconnect between policy and behavior — systems operate within approved access, but outside intended control.
A runtime control plane closes this gap by ensuring trust is evaluated at each action. This requires:
Continuous identity verification
Dynamic credential issuance
Enforcement at the point of interaction
In practice, this means coordinating identity and access as a single system. IBM Verify establishes who or what is acting, Vault issues task-scoped credentials, and Boundary brokers and governs access to target systems. Together, these components shift security from static approval to real-time control, where trust is not assumed, but is continuously proven through action.
»Continuous trust in practice
In an agentic environment, systems don’t operate within fixed boundaries. They act continuously, adapt in real time, and evolve access as they go.
Trust is no longer something you establish once and revisit periodically. It is something you evaluate continuously.
Adopting this model requires rethinking where and how security controls are applied. Identity can no longer be treated as a one-time decision, access can no longer persist beyond the task, and enforcement can no longer sit outside the flow of execution. Instead, these controls need to operate together at runtime and align with system behavior.
Organizations that continue to rely on static roles, long-lived credentials, and checkpoint-based validation will find it increasingly difficult to maintain control as agentic systems scale. However, those that move toward continuous identity verification, dynamic access, and real-time enforcement will be better positioned to manage both the speed and complexity of autonomous systems.
Implementing this model requires bringing identity, credentials, and access enforcement into alignment by adopting platforms like IBM Verify, HashiCorp Vault, and Boundary, which are to provide that support.
Get more insights on securing AI agents with continuous identity and runtime control.







