Traditional IAM was designed for deterministic users and workflows. Agentic AI introduces autonomous, non-deterministic actors that require a fundamentally different authorization model, one that combines identity, delegation, runtime policy evaluation, and ephemeral authorization. AI agents require more than access controls; they need access to map closely to their identity via authorization that is temporary and tightly scoped to a specific request’s transaction context.
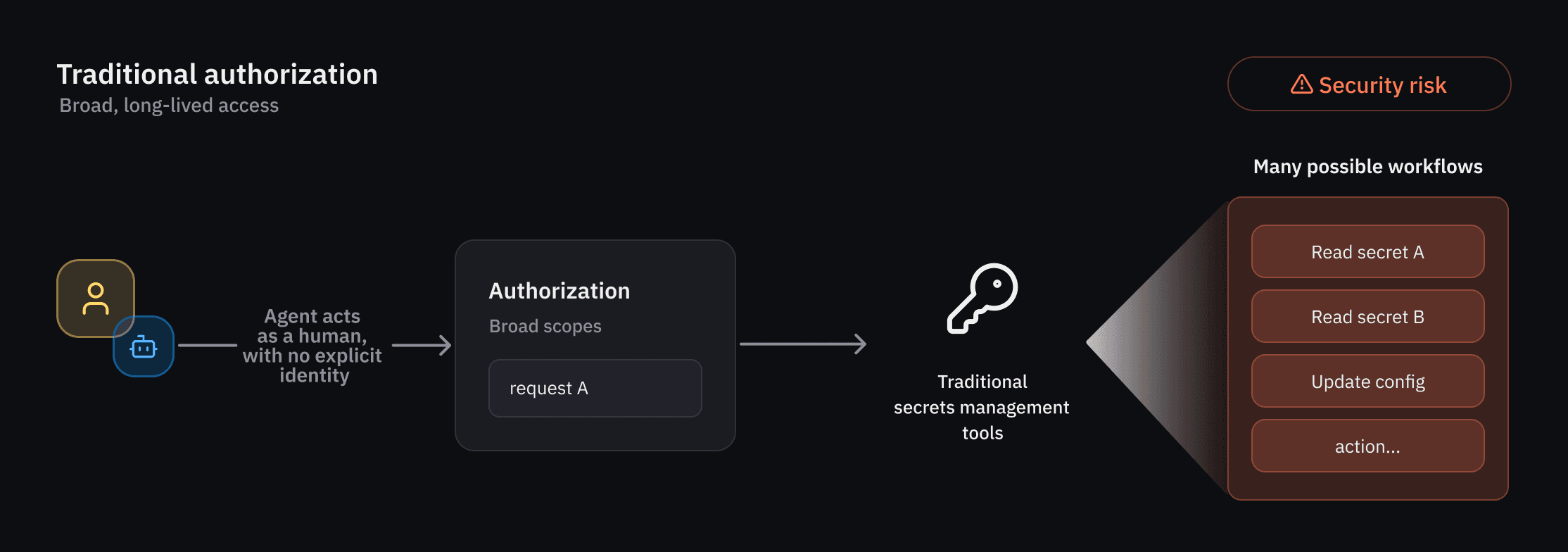
Figure 1: Traditional IAM models grant broad, long-lived access, creating security risks when agents act without an explicit identity.
As organizations adopt AI agents across their environments, HashiCorp Vault customers are increasingly looking for new identity and security controls designed specifically for autonomous systems, including:
The ability to enforce guardrails for agents that operate less predictably than humans or traditional NHIs
Fine-grained authorization that can be evaluated at runtime and scoped to individual actions or workflows
Clear attribution and auditability for actions performed on behalf of users
A standardized approach for securing AI agents across environments and workflows
The unique operational and security characteristics of AI agents led us to build new capabilities in Vault designed specifically for agentic workflows. These capabilities include an agent registry, granular identity-based policies for agents, and per-request authorization (ephemeral authorization) controls to reduce risk by granting temporary access rights that expire after a specific task or timeframe. Select customers are currently evaluating these capabilities through an early access program, with broader public beta availability planned for a future Vault release this summer.
»Agentic identities: a new primitive in Vault’s agent registry
The agent registry allows developers to register and manage agent activity separately from human and traditional non-human identities (NHIs). This agent-specific oversight is particularly critical in delegation flows, where an agent utilizes an on-behalf-of (OBO) pattern from a human user with delegation and consent. By ensuring that this delegation is explicitly tracked, the agent registry forms the starting point for a dedicated framework of registration, authorization, credential management, and observability.
»Enforcing granular identity-based policies
Least privilege access is a top priority for organizations today, and this is especially true when it comes to agents. Vault addresses this through a rich set of policy-based runtime controls that allow administrators to strictly govern agent activity. Because agent behavior can be non-deterministic, we apply deterministic guardrails and per-request access control. Additionally, because agents often operate in delegation mode – carrying the authority of a human user – Vault must evaluate trust across multiple dimensions as agents use Vault to carry out actions like accessing secrets and credentials for target systems.
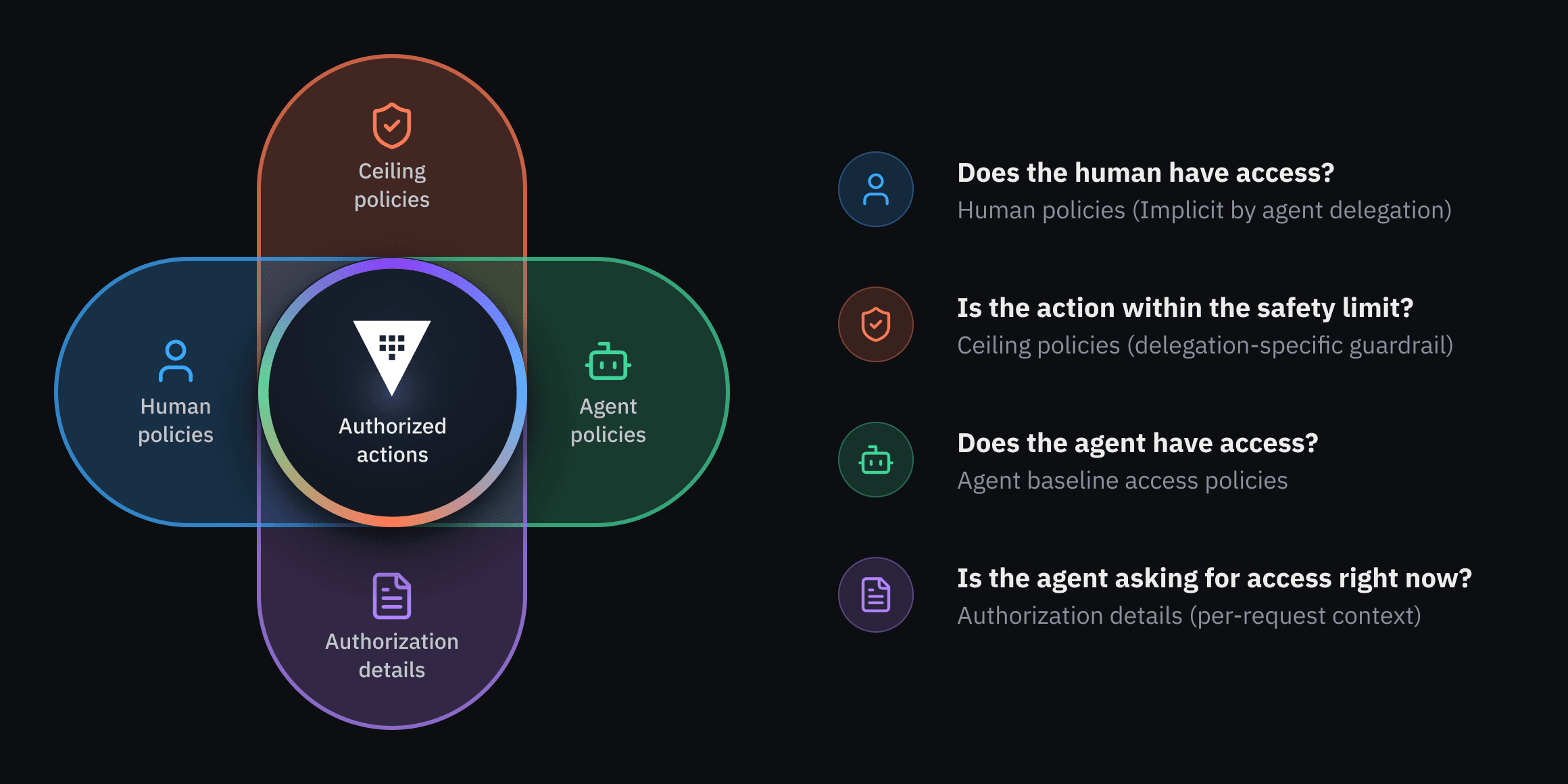
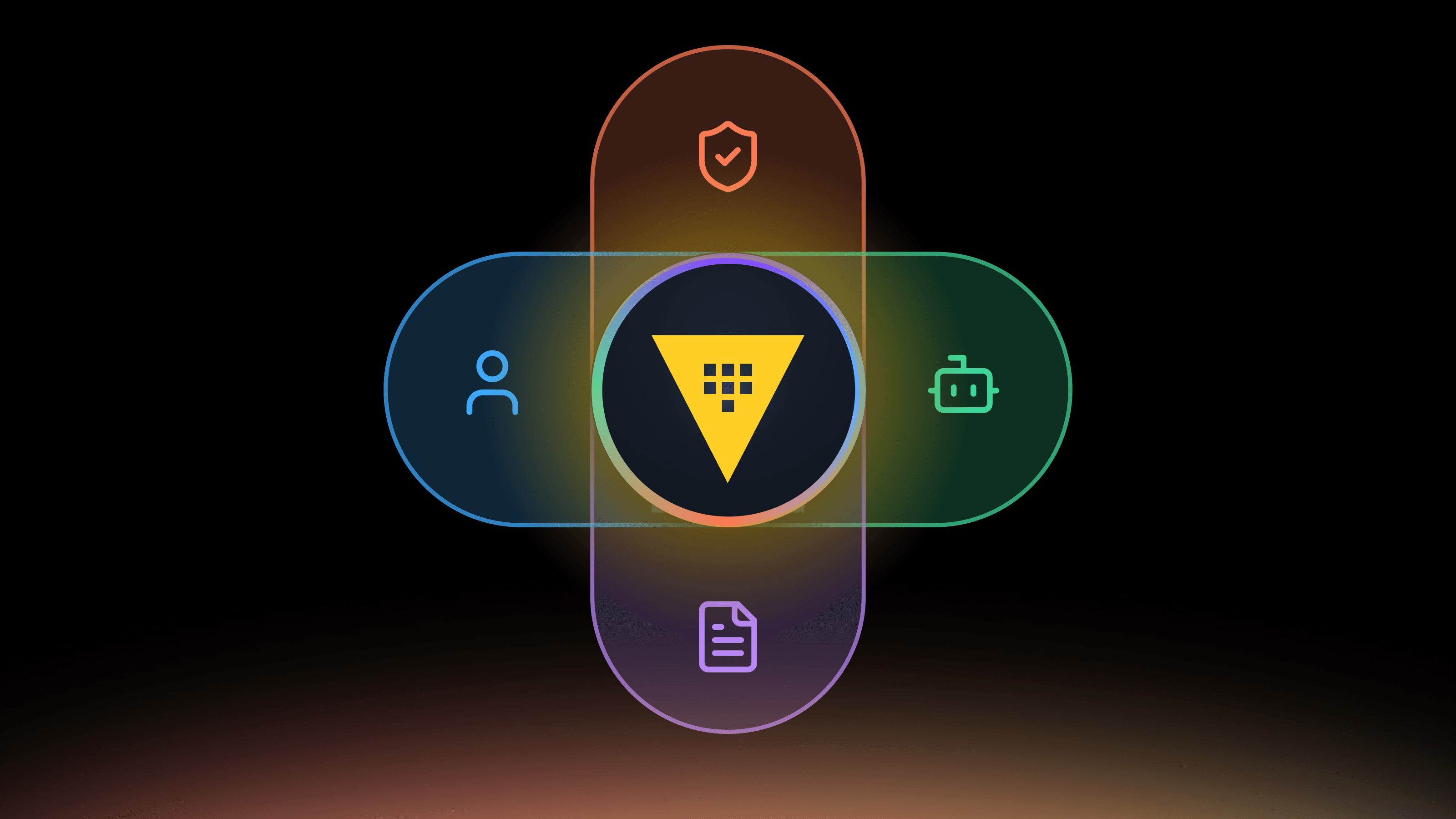
Figure 2: Authorized actions are determined by the intersection of human, agent, and ceiling policies, as well as per-request authorization details.
In this model, authorization is determined by the intersection of three policy layers: the human owner’s policies, the agent’s baseline access policies, and a set of overriding ceiling policies. These ceiling policies apply specifically to delegation flows and establish an absolute blast radius, defining the maximum permissions an agent can ever possess when acting on behalf of a human, regardless of other settings. Much like a Venn diagram, an action is only permitted if it exists within the intersection of these policy sets.
»Ephemeral authorization: scoping access to each agentic request
The policy intersection defines the maximum set of actions an agent can take. In addition, Vault now supports per-request authorization to provide tight scopes for agents, a capability built into the authorization token (based on OAuth 2.0 Rich Authorization Request specification). This addition of transaction context works in concert with ceiling policies, allowing customers to limit what access credentials are granted on a per-request basis to avoid the risk of over-authorization.
To enable ephemeral authorization, the Authorization Server specifies a set of permissions in the authorization_details claim of the JWT’s body. This binds the permission to the token’s lifecycle rather than the agent’s identity, so when the token expires, the agent cannot take further action. This provides per-request resource control that is more secure than entity-based policies alone. Rather than issuing broadly scoped standing permissions, Vault evaluates authorization in the context of a specific request or workflow.
As an illustration, the following JWT claim could be set to allow access to a specific secret in a Vault KV mount called ‘secrets’:
"authorization_details": [
{
"action": "read",
"path_constraint": "secrets/my-secret",
"type": "vault:path_access"
}
],
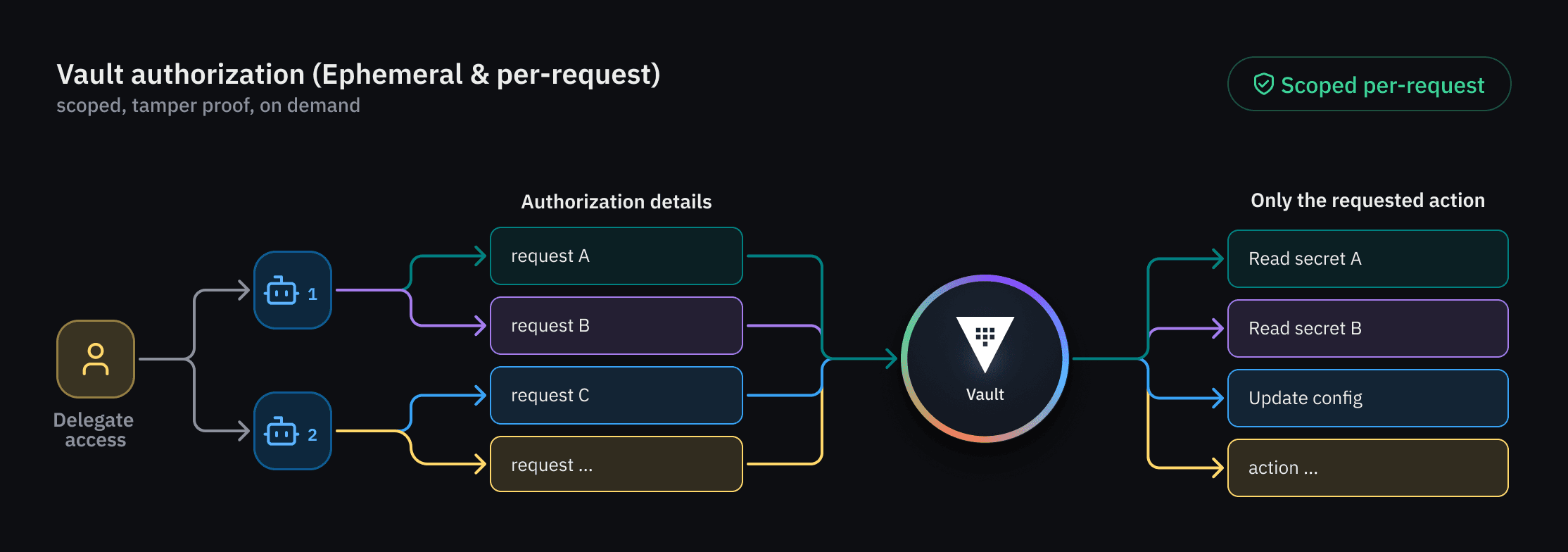
Figure 3: Vault utilizes ephemeral, per-request authorization to tightly scope AI agent access on demand.
Vault can evaluate tamper-proof, per-request authorization details that are part of the authorization token itself. This means that authorization can be scoped to a single request or a single workflow, instead of all possible workflows. Because this model removes the need for a separate token exchange, it reduces operational complexity and simplifies tracking agents' actions.
»Learn more
As AI agents move into production systems, static secrets and broad API tokens are no longer sufficient. Organizations now require runtime identity, bounded delegation, and authorization models designed for autonomous actors. Vault’s emerging agentic identity capabilities secure this transition by ensuring that each agent action is attributable to a specific identity, auditable, and governed by real-time enforcement. This expands Vault’s role from managing secrets and machine identities to governing runtime trust for autonomous systems. Learn more on our use case page.
Native support for AI agents in Vault is currently available to a limited set of customers through an early access program. We expect these capabilities to enter public beta this summer in HashiCorp Vault, so check back soon for additional updates and availability details.